- Research
- Open access
- Published:
Energy-efficient stable routing using QoS monitoring agents in MANET
EURASIP Journal on Wireless Communications and Networking volume 2015, Article number: 13 (2015)
Abstract
In mobile ad hoc network (MANET), the most important issue is to provide a stable and reliable route for the uninterrupted communication. In order to overcome these issues, in this paper, we propose a stable and energy-efficient routing technique. In the proposed method, quality of service (QoS) monitoring agents collect and calculate the link reliability metrics such as link expiration time (LET), probabilistic link reliable time (PLRT), link packet error rate (LPER) and link received signal strength (LRSS). In addition, residual battery power (RBP) is implemented to maintain the energy efficiency in the network. Finally, route selection probability (RSP) is calculated based on these estimated parameters using fuzzy logic. Simulation results show that the proposed routing technique improves the packet delivery ratio and reduces the energy consumption.
1 Introduction
A mobile ad hoc network (MANET) is a collection of wireless nodes that is self-configured to form a network without the aid of any established infrastructure. The nodes are mobile and their movement is random. Each host in this network must have the ability to work as a router. The host mobility changes the quality of wireless link signals because of the changes in the propagation path loss, shadowing effect, multipath fading, and interference. This leads to the link failure and breaks all the routes that use this link. MANET needs an efficient adaptive routing protocol because of its highly dynamic topology.
Ad hoc networks have to face several challenges, such as dynamic topology, real-time communication, resource constraint, bandwidth management and packet broadcast overhead. These issues complicate the network to design the routing protocols. There have been many routing protocols developed for MANET over the past few years. The primary routing protocols for MANET consume considerable amount of the limited amount of battery power present in the nodes. Thus, routing in MANET is very much energy-constrained [1].
The examples are Destination-Sequenced Distance-Vector (DSDV) routing, Dynamic Source Routing (DSR) protocol, and ad hoc on-demand vector (AODV) protocol [2-5].
To meet the QoS requirements of mobile users, several metrics like route stability can be considered for selecting a source destination routing path. Route stability focuses on the following aspects:
-
Stable routes: To maximize the throughput and reduce the traffic latency, reliable source-destination connections must be ensured over time. A route is selected based on the node’s motion and probability model of the path future availability.
-
Efficient route repair: If the path duration estimate is available, service disruption due to route failure can be avoided by creating an alternative path before the current path breaks. Note that the presence of path duration information avoids the wastage of radio resources due to the reallocations of backup paths.
-
Network connectivity: Connectivity and topology characteristics determined by the link dynamics are fundamental issues to network design, as they determine the system capability to support user communications and their reliability level [6].
Stability-based routing protocols tend to select paths that are long lasting. Signal strength, pilot signals and relative speed between nodes are the parameters used for the computation of link stability. The number of links that compose the route and the stability of each link in the route determine stability or lifetime of a route. Hence, the probability of route failure can be reduced by reducing either the link failure rate or the number of links that compose the route [7]. Designing an effective and efficient fault-tolerant routing protocol is inherently hard since the precise path information is unavailable [8,9].
The cross-layer paradigm makes the routing layers by interacting efficiently and estimating the link stability. A Cross-layer-Based Multipath Routing (CBMR) protocol improves QoS. TCP over wireless networks needs to be cross-layer designed, which depends on the information of MAC [10]. Cross-layer design allows the interaction between any layers. QoS provisioning is one of the most important areas. Examples of cross-layer design for QoS provisioning in MANETs include an adaptive service model utility fair, an adaptive resource management architecture, TIMELY, etc. [11].
A cross-layer approach makes the routing layer more robust. The routing layer, link layer and physical layer cooperate to gain better result. The physical layer provides power information or a signal-to-interference-plus-noise ratio (SINR) to the routing layer, and the routing layer decides the neighbour nodes’ level using it and computes the backoff time and data rate for the link layer using the node’s level. The link layer uses the backoff time, data rate and data count information provided by the routing layer to decide a packet whether it transmits or not. The routing stability of a MANET is improved by this cross-layer model [12-14].
1.1 Main contribution
In our previous work [15], a joint design of routing and resource allocation using QoS monitoring agents was proposed. In this joint design, depending on the bandwidth request, a QoS monitoring agent checks the available bandwidth and allocates the resources temporarily for the real-time flows. In case of QoS changes or route breakages, the monitoring agent sent a feedback to the source, which contains the estimated amount of resources to be reserved or the route failure information. The sender adaptively adjusts the reservations or data rate when there is a QoS change or selects another efficient route when there is a route or link failure.
As route stability and energy efficiency are the two major issues of routing in MANET, this paper aims to provide stability and energy efficiency to the existing routing protocol using fuzzy logic decision model.
2 Literature review
Weng and Yang [3] have proposed a cross-layer stability-based routing mechanism for ultra wideband networks (LS_AODV) where a computing model is established to map the received signal strength into link stability factor and route stability factor, which serves as a routing metric for path selection. The received signal strength can be used to reveal the link state information for grey zone prediction and route state monitoring. A HELLO-based pre-emptive local route repair algorithm prevents the occurrence of link breakage. However, it suffers from too many route breaks and route rediscovery procedures due to the occurrence of communication grey zone.
Yang and Huang [16] have proposed a QoS routing protocol based on link stability with dynamic delay prediction for MANET that makes routing decisions according to link state and dynamic delay detection. In the route discovery phase, it finds the paths with great link stability factor. Thus, a feasible path is selected for data transfer. In the route maintenance phase, it monitors the network topology changes by delay prediction and performs rerouting before the paths become unavailable. It significantly improves the routing performance and guarantees the QoS request. However, the extra computation for link stability factor in SDCR causes the slightly higher delay.
Sargolzaey et al. [17] have proposed a new cross-layer metric (CLM) and compared the efficiency of link reliability metrics for finding reliable links in MANET. It reduces the number of route reconstructions in this network. By using all the metrics, the number of route reconstructions can be reduced. Simulation results show that the metric has the maximum efficiency in all of the network conditions and reduces the number of route reconstructions more than the others. However, the route reconstruction is reduced only up to 50%.
Kagi and Takahashi [18] have proposed an efficient reliability improvement method in MANET by applying network coding encoded by a relay node. Reliability is improved without requiring the source node to send redundant encoding packets. Simulations show that the packet delivery ratio of this work is higher than that of packet-level forward error control (FEC) but has longer delay in environment with packet errors. By decreasing the number of packets transmitted by the source, the packet overhead is improved. Thus, this method realizes more efficient and reliable data transmission. However, FEC that sends both the data and encoding packets has higher packet overhead.
Rubin and Zhang [19] have proposed robust throughput capacity measures to provide highly survivable transport of flows. To provide a robust throughput transport service for flows, a new scheme that implements a robust flow admission and routing scheme is presented. Their on-demand robust routing algorithm selectively discovers routes that are probabilistically assured to survive for the duration of the underlying sessions or file transfers. However, due to lack of link capacity resources, flows that could have been routed across sufficiently robust routes cannot be accommodated and are blocked.
Zahedi and Ismail [20] have proposed the route maintenance approach for link breakage prediction to avoid link breakages in MANET. The received signal strength indicator value predicts a link breakage in its link with its next hop to the source node of this active route. It reduces the probability of constructing a route with bad links and then increases the packet delivery ratio with less packet loss and end-to-end delay. Hence, the performance of the protocol is increased. However, the decrease in the transmission range of nodes of the route reduces the efficiency where link breakages will so frequently occur.
Misra et al. [21] have considered the problem of location updating in MANETs. They have proposed a node stability-based location updating approach. They have compared its performance with that of the performance of the conventional location updating algorithm. They obtained different types of results by varying different parameters such as the number of nodes and the terrain dimensions.
Dhurandher et al. [22] have proposed an energy-efficient ad hoc on-demand routing (EEAODR) algorithm that balances energy load among nodes so that a minimum energy level is maintained among nodes and the network life is increased.
Misra et al. [23] have proposed a learning automata-based fault-tolerant routing algorithm (LAFTRA). It performs routing with faulty nodes in MANETs using multipath routing. The theory of learning automata (LA) has been used for optimizing the selection of paths, reducing the overhead in the network, and for learning about the faulty nodes present in the network.
3 Energy-efficient stable routing using QoS monitoring
3.1 Overview
In this technique, the QoS monitoring agents collect and estimate the link reliability metrics link expiration time (LET), probabilistic link reliable time (PLRT), link packet error rate (LPER) and link received signal strength (LRSS) [17] in order to ensure stable routing. These metrics are used to find reliable links in MANET. In addition, they reduce the number of route reconstructions in the wireless network. Next, the residual battery power (RBP) of a node is also estimated for providing energy conservation.
In stable multipath route discovery phase, an enhanced stable path collection mechanism based on source routing and adaptive ad hoc on-demand multipath distance vector (AOMDV) is designed to discover multiple paths between the source and the destination. For selection of optimal routes, a fuzzy logic-based selection technique is applied. Here, the LET, PLRT, LPER and LRSS and RBP are taken as input for the fuzzy logic engine and based on the results of fuzzy rules, the route selection probability is estimated as output.
In pre-emptive route repair phase, the moving node, which is responsible for the occurrence of communication grey zone, is detected based on the above designed metrics. An appropriate node is selected to do route repair and start fast local route repair. A hybrid strategy using two key methods HELLO scheme and position location scheme is employed to gather topological information for pre-emptive route repair (Figure 1) [3].
3.2 Estimation of metrics
In this section, in order to find the reliable routes in the network, we estimate LET, PLRT, LPER, LRSS and RBP, which are related to the links between the nodes.
3.2.1 Link expiration time [17]
LET metric is related to the reliable routes in the network. In order to estimate the LET between the nodes, the free space propagation and the motion parameters of two neighbouring nodes are required. Using motion parameters of two neighbouring nodes, it is possible to calculate the period of two nodes connected in the network. Let us consider that the two nodes in the network have the same transmission radius R and let (x 1, y 1) and (x 2, y 2) denote the positions of the nodes. Also, let us consider v 1 and v 2 denote the speed of the nodes along with θ 1 and θ 2 as directions, respectively. Then, the LET is given by the following equation below:
where a = v 1 cos θ 1 − v 2 cos θ 2, b = x 1 − x 2, c = v 1 sin θ 1 − v 2 sin θ 2 and d = y 1 − y 2.
3.2.2 Probabilistic link reliable time [17]
Another link reliability metric from the network layer is PLRT. To compute PLRT, simulation experiments must be run for the unreliable base protocol. During these simulations, the lifetime of the links is measured and the average lifetime of the links is computed. Then, the link reliability is computed as:
where ρ is the inverse of this lifetime and which also represents the average link failure rate in the network. t is the time during the link at work.
3.2.3 Link packet error rate [17]
The best metrics for reliability of a wireless link are signal-to-noise ratio (SNR) and bit error rate (BER) of the link. Unfortunately, these metrics cannot be obtained for each received frame in realistic scenarios. However, another metric LPER, which is related to these two metrics, can be obtained. It is a data link layer metric for link reliability. LPER can be computed by finding the number of damaged receiving packets (packets received with error) in a time interval and normalizing it by the time interval duration. Note that for this metric:
-
i.
Higher value means lower reliability,
-
ii.
It must be transferred to the network layer for using in the routing protocols.
3.2.4 Link received signal strength
The physical layer received signal strength is another good metric for reliability of a link [16]. For obtaining this metric, we must have the received signal strength measurement at the physical layer. Like LPER, this metric must also be transferred to the network layer.
3.2.5 Residual battery power [24]
In wireless networks, the power conservation is the main issue as the energy and power are limited in the networks. So, it is important to conserve the node’s energy using routing algorithms and selecting alternative routes in the network. Normally, during the transmission of the data packets in the network, sometimes the nodes may consume more or less energy, for example, when an intermediate node has been elected as a router where the router may consume more energy than a normal node in the network. Hence, the major aim of energy-aware routing is to consider the routes according to the battery power status of the nodes present in the network.
where
RBPn denotes node n’s residual battery power at a certain time period T.
R 0 denotes the intrinsic energy power of the unit.
R t denotes the different energy power values at different times.
T denotes the instant at which this residual energy is estimated.
3.3 Stable multipath route discovery algorithm
In this section, we will apply the multipath collection algorithm based on source routing and AOMDV.
Here, route request (RREQ) packets maintain the complete information about the entire paths included between the source and destination.
Generally, the route searching process ends up with the shortest path with longer route which are unstable links or shorter links with longer route which are stable route. The main aim of our route discovery method is to discover the stable route. The proposed algorithm has three detection methods to end with stable path. The reverse route is updated once all the detections are successfully passed. Here, we denoted hop count of RREQ message as (rq_hop_count) and advertised hop count (rq_advertised_hops).
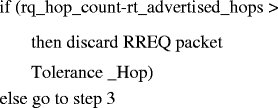
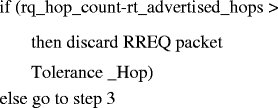
The algorithm can be explained in the following steps:
-
Step 1: In the first step of route discovery procedure, gray zone detection technique is implemented to ensure that discovered link will be stable in the near future.

-
Step 2: Hop count detection technique avoids the unnecessary long paths by using a parameter called as ‘tolerance hop’.
-
Step 3: In loop-free detection technique, when RREQ packet is received, the node checks about the routing information, which is included in RREQ (N1_address is the address of node which is checking the routing information in RREQ packet, and N1_address_RREQ is the address of N1 in the RREQ packet).

-
Step 4: After that, reverse route table is updated with RREQ message. After the table is updated, link stability factor (LSF) of this link is inserted to Reverse_LSF_list for recording the LSF value of each link along the reverse path.
-
Step 5: If current node (N1) = destination (D),

In Figure 2 according to the route acceptance rule of AOMDV, when node I obtains the RREQ through node A first, then it discards the copy of RREQ from C without creating a reverse path. In this case, RREQ is received at node D first through node X; then, the only path which is built is (S-A-I-J-D).
Whereas, the reverse path through C can be accepted according to the proposed looser route acceptance and hence two routes can be discovered, which are (S-A-I-J-D) and (S-B-C-I-K-D).
3.4 Fuzzy-based reliable route selection algorithm
3.4.1 Fuzzy logic system
Figure 3 demonstrates the fuzzy logic system (FLS) that involves the selection of optimal path for data transmission. This is performed by considering the inputs LET, PLRT, LPER, LRSS and RBP. These inputs are fuzzified to obtain the appropriate optimal path.
The steps that determine the fuzzy logic system are as follows:
-
Fuzzification: The process of getting the crisp inputs from the chosen input variables and estimating the degree to which the inputs belong to each of the appropriate fuzzy sets is termed as fuzzification.
-
Inference system: In this step, the fuzzified inputs are taken and applied to the antecedents of the fuzzy rules. It is then applied to the consequent membership function. Finally, the outputs of all rules are merged.
-
Defuzzification: In this step, the merged output of the aggregate output fuzzy set is taken as input, and a single crisp number is obtained as output.
3.4.2 Fuzzification
This involves fuzzification of input variables such as LET, PLRT, LPER, LRSS and RBP. The crisp inputs are taken from these variables, and these inputs are given a degree to appropriate fuzzy sets. The crisp inputs are combination of LET, PLRT, LPER, LRSS and RBP. The output variable route selection probability (RSP) is also represented as a triangular fuzzy set. We take three possibilities, high, medium and low for input and output variables.
Figures 4, 5, 6, 7, 8 and 9 show the membership function for the variables LET, PLRT, LPER, LRSS, RBP and RSP, respectively. This utilizes the triangulation functions as they are widely used in real-time applications owing to their computational efficiency and uncomplicated formulas.
Table 1 demonstrates the designed fuzzy inference system. This illustrates the function of the inference engine and method by which the outputs of each rule are combined to generate the fuzzy decision.
For example,

3.4.3 Defuzzification
The technique by which a crisp value is extracted from a fuzzy set as a representation value is referred to as defuzzification. The centroid of area scheme is taken into consideration for defuzzification during fuzzy decision-making process. The formula (4) describes the defuzzifier method.
where fuzzy_cost is used to specify the degree of decision-making, f i is a variable for fuzzy all rules and α (f i ) is its membership function.
The output of the fuzzy cost function is modified to crisp value as per this defuzzification method [19]. The defuzzified output gives the route selection probability in terms of percentage.
Hence, the route with high percentage of route selection probability is selected as the optimal route, which will be stable and energy efficient.
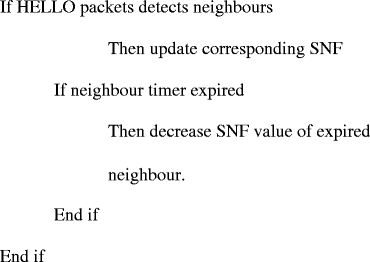
3.5 HELLO scheme-based route repair technique
Once the grey zone is detected, a route repair technique is to be implemented. In this scheme, the HELLO message is extended for neighbour sensing and neighbour set exchanging. It can also be used as an ON/OFF command to control the position location scheme and HELLO scheme of neighbour nodes.
Here, the existing reserved field in HELLO message is used to convey the IP address of the moving node and its next hop that is the destination of pre-emptive route repair is denoted as PN_1, PN_2 (which shows the movement of two adjacent nodes) and PNN_DES.
The reliability is considered according to the RBM along with SNF metrics in the local route repair technique.
A Boolean flag ‘T’ is used with two values, namely, Start_Hello = 1 and Stop_Hello = 0. These values are used as command in order to control the operations of neighbour nodes.
The route repair technique can be explained briefly in the following steps:
-
Step 1: Once the route repair technique is started, the current node (CN) starts broadcasting the HELLO packet with the condition TTL >1 and T = START_HELLO. Here, the TTL defines the size of regions which is under route repair and is not fixed.
-
Step 2: Once the neighbour node OF CN receives the HELLO packet with TTL >1 and P = START_HELLO, it starts the position scheme, which ranges towards the HELLO source and broadcasts the HELLO packet consequently. The generated HELLO packet is then again initialized with TTL = 1. Hence, only the node in the range (TTL-1) participates in position location process, and it helps in energy saving.
-
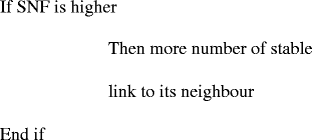
Step 3: In the next step, gathering of topology information is done based on the stability metrics that consider the history records of neighbours. Hence, stable neighbour frequency (SNF) is implemented. In the route repair technique, every node records the collective times of a node as its neighbour, which is represented as SNF.
-
Step 4: The neighbour sets, which are associated with SNFs, are exchanged between neighbours.
-
Step 5: After that, the neighbour with SNF value 0 is removed, and high-speed moving node is filtered from CN for route reconstruction.
-
Step 6: Once the node is selected for recovery process, the reconstruction of the path starts. The latest discovered neighbour set is used for exchanging neighbourhood information, which includes SNF values and corresponding link lengths.
-
Step 7: A stable path is selected from the candidate paths, which are collected by travelling through the latest N-hop_nb_list. Paths with larger SNF values and shorter length are considered more stable than others.
-
Step 7: In case there are candidate paths, which are suitable for route repair, one path is selected randomly. Once alternate path is determined, the source routing information of the reconstructed path to PNN_DES is added in N-hop HELLO packet with T = STOP_HELLO where N denotes path length. Each node which receives such packet must stop HELLO and position location method.
-
Step 8: In case of intermediate node along this path, route table entry corresponding to destination is created or updated consequently. In this way, a new path is reconstructed before the link breaks.
-
Step 9: If no alternate path is available, the local route repair will be considered as ‘failed’ (Tables 2 and 3, Figure 10).
Table 2 Topology information gathered by node B Table 3 HELLO extension as command
4 Simulation results
4.1 Simulation model and parameters
We use NS2 [25] to simulate our proposed Energy Efficient Stable Routing Using QoS Monitoring Agents (EESRQMA) technique. In our simulation, the channel capacity of mobile hosts is set to the same value: 2 Mbps. We use the distributed coordination function (DCF) of IEEE 802.11 for wireless LANs as the MAC layer protocol. It has the functionality to notify the network layer about link breakage.
In our simulation, the mobile nodes move in a 1,000 × 1,000 m region for 50-s simulation time. All nodes have the same transmission range of 250 m. The number of nodes is varied from 25 to 50, and node speed is varied from 5 to 25 m/s.
Our simulation settings and parameters are summarized in Table 4.
4.2 Performance metrics
We evaluate mainly the performance according to the following metrics.
Average packet delivery ratio: It is the ratio of the number of packets received successfully and the total number of packets transmitted.
Delay: It is the time taken by the packet to reach the receiver.
Residual energy: It is the average residual energy of the communicating nodes.
We compare our EESRQMA technique with that of the Cross-Layer Metric-Based Location Aided Routing (CLM-LAR) protocol [17]. The simulation results are presented in the next section.
4.2.1 Based on number of nodes
Initially, the number of nodes is varied as 25, 30, 35, 40, 45 and 50. The node speed is kept at 5 m/s. There are eight traffic connections from random source and destination pairs including constant bit rate (CBR), video and transmission control protocol (TCP) traffic.
The end-to-end delay measured for both the techniques in the varying node scenario is shown in Figure 11. It shows that the increase in number of nodes can increase the delay, since the number of hops increases. The figure clearly shows that EESRQMA obtains 29% lesser delay than CLMLAR.
The packet delivery ratio obtained for both techniques in the varying node scenario is depicted in Figure 12. It shows that the increase in number of nodes can decrease the delivery ratio, since the number of hops increases. It can be seen from the figure that EESRQMA obtains 33% higher delivery ratio than CLMLAR.
Figure 13 shows the residual energy measured for both the techniques in the varying node scenario. It can be seen that EESRQMA has 7% more residual energy than CLMLAR.
4.2.2 Based on node speed
Next, the node speed is varied from 5 to 25 m/s while keeping the number of nodes as 50. There are eight traffic connections from random source and destination pairs including CBR, video, and TCP traffic.
The end-to-end delay measured for both the techniques for the varying speed scenario is shown in Figure 14. It shows that increase in node speed can increase the delay, since there will be more route disconnections. The figure shows that EESRQMA obtains 33% lesser delay than CLMLAR.
The packet delivery ratio obtained for both techniques in the varying speed scenario is depicted in Figure 15. It shows that the increase in number of nodes can decrease the delivery ratio, since there will be more route disconnections. It can be seen from the figure that EESRQMA obtains 58% higher delivery ratio than CLMLAR.
Figure 16 shows the residual energy measured for both the techniques in the varying speed scenario. It can be seen that EESRQMA has 8% more residual energy than CLMLAR.
5 Conclusions
In our proposed solution, we implemented a cross-layer based stable and energy-efficient routing technique in which QoS monitoring agents collect and calculate the link reliability metrics such as LET, PLRT, LPER and LRSS. These types of metrics help to find the most reliable link and reduce the number of route reconstructions in wireless network. In addition, RBP is implemented that helps to maintain the energy efficiency in the network. Finally, RSP is calculated based on these estimated parameters using fuzzy logic. Simulation results show that the proposed routing technique improves the packet delivery ratio and reduces the energy consumption.
References
S Misra, SK Dhurandher, MS Obaidat, P Gupta, K Verma, P Narula, An ant swarm-inspired energy-aware routing protocol for wireless ad-hoc networks. J. Syst. Softw. 83, 2188–2199 (2010)
A Dana, A Mansour, YM Hajhosseini and T Mirfakhraie, A robust cross-layer design of clustering-based routing protocol for MANET. in ICACT 2008, Gangwon-Do, 17–20 Feb 2008.
L-N Weng and J Yang, A Cross-layer Stability-Based Routing Mechanism for Ultra Wideband Networks (Elsevier B.V., 2010).
F Ducatelle, G Di Caro, LM Gambardella, Using ant agents to combine reactive and proactive strategies for routing in mobile ad-hoc networks, Technical Report No. IDSIA-27-04-2004, September 2004, World Scientific.
P Bose, P Morin, I Stojmenovic, J Urrutia, Routing with guaranteed delivery in ad hoc wireless networks. ACM Wireless Netw. 7(6), 609–616 (2001)
G Carofiglio, C-F Chiasserini, M Garetto, EL, Route stability in MANETs under the random direction mobility model. in IEEE Transactions on Mobile Computing, Gangwon-Do, Sept 2009.
S Nityananda, N Sukumar, Route Stability Based QoS Routing in Mobile Ad Hoc Networks (Springer Science+Business Media, LLC, 2009)
Y Xue, K Nahrstedt, Fault Tolerant Routing in Mobile Ad Hoc Networks (Proc. IEEE WCNC, New Orleans, 2003), pp. 1174–1179
S Misra, SK Dhurandher, MS Obaidat, K Verma, P Gupta, A low overhead fault-tolerant routing algorithm for mobile ad-hoc networks based on ant swarm intelligence. Simul. Model. Pract. Theor. 18(5), 637–649 (2010)
S Venkatasubramanian, A cross-layer based multipath routing protocol to improve QoS in mobile ad hoc networks. ACEEE Int. J. Netw. Sec. 1(1), 42–48 (2010)
B Zhou, A Marshall, T-H Lee, A cross-layer architecture for DiffServ in mobile ad-hoc networks. in 2005 International Conference on Wireless Networks, Communications and Mobile Computing, 13–16 June 2005.
X Wu and Y Cao, Cross Layer Multicasting Protocol in Ad Hoc Networks (IEEE, Xi’an, 2011).
S Misra, PV Krishna, V Saritha, LACAV: an energy-efficient channel assignment mechanism for vehicular ad hoc networks. J. Supercomput. 62(3), 1241–1262 (2012)
VD Park, MS Corson, A highly adaptive distributed routing algorithm for mobile wireless networks. Proc. INFOCOM 97, 1405–1413 (1997)
P Senthilnathan, C Kalaiarasan, A joint design of routing and resource allocation using QoS monitoring agent in mobile ad-hoc networks. J. Theor. Appl. Inf. Technol. 55, 224–231 (2013)
P Yang and B Huang, QoS routing protocol based on link stability with dynamic delay prediction in MANET. in 2008 IEEE Pacific-Asia Workshop on Computational Intelligence and Industrial Application (IEEE, Wuhan, 2008).
S Hadi, A Borhanuddin Mohd, K Sabira, A Cross Layer Metric for Discovering Reliable Routes in Mobile Ad Hoc Networks (Springer Science+Business Media, LLC, Xi’an, 2011).
K Tomonori, T Osamu, Efficient Reliable Data Transmission Using Network Coding in MANET Multipath Routing Environment (Springer-Verlag, Heidelberg, 2008)
I Rubin and R Zhang, Robust Throughput and Routing for Mobile Ad Hoc Wireless Networks. Ad Hoc Networks 7 (Elsevier B.V, 2009).
K Zahedi, AS Ismail, Route maintenance approach for link breakage prediction in mobile ad hoc networks. IJACSA 2, 10 (2011)
S Misra, SK Dhurandher, MS Obaidat, N Nangia, N Bhardwaj, P Goyal, S Aggarwal, Node stability-based location updating in mobile ad hoc networks. IEEE Syst. J. 2(2), 237–247 (2008)
SK Dhurandher, S Misra, MS Obaidat, V Bansal, P Singh, V Punia, An energy-efficient on-demand routing algorithm for mobile ad-hoc networks, in Proceedings of the 15th IEEE International Conference on Electronics, Circuits and Systems (IEEE ICECS 2008), St. Julians, Malta, 31 Aug–3 Sept 2008, pp. 958–961
S Misra, PV Krishna, A Bhiwal, AS Chawla, BE Wolfinger, C Lee, A learning automata-based fault-tolerant routing algorithm for mobile ad hoc networks. J. Supercomput. 62(1), 4–23 (2012)
RA Mallah, A Quintero, A light-weight service discovery protocol for ad hoc networks. J. Comput. Sci. 5(4), 330 (2009)
Network Simulator, http://www.isi.edu/nsnam/ns.
Author information
Authors and Affiliations
Corresponding author
Additional information
Competing interests
The authors declare that they have no competing interests.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made.
The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder.
To view a copy of this licence, visit https://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Palaniappan, S., Chellan, K. Energy-efficient stable routing using QoS monitoring agents in MANET. J Wireless Com Network 2015, 13 (2015). https://doi.org/10.1186/s13638-014-0234-9
Received:
Accepted:
Published:
DOI: https://doi.org/10.1186/s13638-014-0234-9