- Research Article
- Open access
- Published:
Tree Based Protocol for Key Management in Wireless Sensor Networks
EURASIP Journal on Wireless Communications and Networking volume 2010, Article number: 910695 (2010)
Abstract
Securing a wireless communication has generally a vital importance, particularly when this communication is in a hostile environment like in wireless sensor networks (WSNs). The problem is how to create cryptographic keys between sensor nodes to ensure secure communications. Limited resources of sensor nodes make a public key cryptosystem such as RSA not feasible. So, most solutions rely on a symmetric cryptosystem. In this paper, we propose a new key management scheme based on symmetric cryptography which is well adapted to the specific properties of WSNs. The evaluation of our solution shows that it minimizes memory occupation, ensures scalability, and resists against the hardest attack: compromised nodes.
1. Introduction
The convergence of technological advances in microelectronics and wireless communications has enabled the emergence of a promising area: Wireless Sensors Networks (WSNs). WSNs come from the combination of embedded systems and distributed systems. WSNs have opened the way for a multitude of research areas and the huge interest generated by researchers activities calls for broad fields of applications in the near future.
Sensors appear as miniaturized systems, equipped with a processing unit and storage of data, a unit of wireless transmission and a battery. Organized as a network, the sensors (or nodes) of a WSN, despite resource constraints in computing capacity, storage, and energy, have to play an essential role in quasi all domains of human environment. They are primarily dedicated to collect data from physical phenomena such as monitoring global warming and send them to a base station (also called the sink) [1]. Figure 1 shows an example of a WSN composed of ten sensor nodes deployed randomly around a base station. Depending on the size of the deployment area, the transmission range of the sensor nodes, and the base station, sensor nodes can communicate with the base station directly or indirectly by computing a hop-by-hop route to it. Many barriers to the common deployment of WSNs have to be overcome before they can reach their full maturity. Among these obstacles, the security problem is acute and must be addressed adequately and in accordance with the binding characteristics of WSNs. Because of their constraints and their deployment in unattended and hostile environments, the different nodes of a WSN are vulnerable to node compromising and also to physical damage [2]. In addition, the use of wireless transmission makes WSNs permeable to all sorts of malicious attacks. Consequently, security is a real challenge to rise.
Several key management protocols for WSNs were proposed to respond to the security requirements of these environments. Unfortunately, node compromising is rarely or not enough investigated and most of these protocols have a weak resilience to this attack. In this paper, we present a symmetric-based key management solution for WSNs called STKM (Spanning Tree Key Management for WSN). STKM is a simple and robust solution to secure node-to-node and node-to-base station communications. STKM assumes a random deployment of nodes. It builds a tree that spans all the sensor nodes. This tree allows key refresh with small costs. Simulation results show that STKM is very resilient to node compromise while preserving energy consumption at the level of sensor nodes.
The rest of the paper is organized as follows. First, we discuss related work in Section 2. In Section 3, we present our solution and give its detailed algorithms. Section 4 is devoted to an analysis and a simulation of the proposed solution. Section 5 concludes our work.
2. Background and Motivation
Key management is the process by which cryptographic keys are generated, stored, protected, transferred, loaded, used, and destroyed [3]. Figure 2 lists a selection of existing key management solutions proposed for WSNs in the literature, for a detailed state of the art see [3]. Most existing key management solutions are based on symmetric cryptography mainly because of its reasonable energy consumption. Asymmetric cryptography involves the use of a pair of keys (public key and private key) to encrypt and decrypt messages. Each node in the network has a public and a private key, the first is known throughout the network, the second is secret, that is, known only by the node. The source node encrypts messages using the public key of the destination node, and this latter uses its private key to decrypt received messages. In symmetric cryptography, the source and the destination use the same key to encrypt and decrypt messages. Asymmetric cryptography offers better resistance against node compromise attack and allows scalability but requires an additional part on software and hardware of the nodes. Some researchers investigated asymmetric cryptographic tools and propose adapted solutions. Examples of such solutions are Tiny Public Key (TinyPK) [4] and Tiny Elliptic Curve Cryptosystem (TinyECC) [5].
With symmetric cryptography, the simplest idea is to load a secret information in the sensor nodes before their deployment in the network. This secret information deployed in the network may be the secret key itself or an auxiliary information that helps nodes to derive the real secret key shared by the nodes. With this secret key, nodes can securely exchange messages [3]. The main disadvantage of this solution is that compromising one node (access to the preloaded key) might lead to compromise the entire network. To overcome this limitation, several researchers propose schemes that establish pairwise keys rather than a unique global key. For example in [6], the authors focus on developing cost-saving mechanisms while weakening the threat model. They propose Key Infection, a lightweight security protocol suitable for use in noncritical commodity sensor networks where an attacker can monitor only a fixed percentage  of communication channels. With Key Infection, a node wishing to communicate securely with other nodes simply generates a symmetric key and sends it in the clear to its neighbors.
of communication channels. With Key Infection, a node wishing to communicate securely with other nodes simply generates a symmetric key and sends it in the clear to its neighbors.
In [7], Blon describes a Key-matrix-based dynamic key generation solution. In this solution, some of the possible link keys in a network of size N are represented as a  key matrix. The scheme stores small amount of information in each sensor node, so that some pair of nodes can calculate corresponding field of the matrix, and uses it as the link key. This solution is
key matrix. The scheme stores small amount of information in each sensor node, so that some pair of nodes can calculate corresponding field of the matrix, and uses it as the link key. This solution is  -secure, meaning that keys are secure if no more than
-secure, meaning that keys are secure if no more than  nodes are compromised.
nodes are compromised.
Another  -secure solution is presented in [8] and called Polynomial-based key predistribution scheme. This scheme distributes a polynomial share (a partially evaluated polynomial of degree
-secure solution is presented in [8] and called Polynomial-based key predistribution scheme. This scheme distributes a polynomial share (a partially evaluated polynomial of degree  ) to each sensor. So, each sensor node stores a polynomial with
) to each sensor. So, each sensor node stores a polynomial with  coefficients and every pair of sensor nodes can establish a key using the property of symmetry of polynomials. The solution is
coefficients and every pair of sensor nodes can establish a key using the property of symmetry of polynomials. The solution is  -secure, meaning that coalition of less than
-secure, meaning that coalition of less than  sensor nodes knows nothing about pairwise keys of others.
sensor nodes knows nothing about pairwise keys of others.
In [9], the authors propose BROSK (BROadcast Session Key negotiation protocol). With BROSK every node broadcasts a message containing its nonce. So, every two neighboring nodes that hear each other can compute a common key which is function of their two nonces. Neighboring nodes authenticate themselves with a predeployed key which is supposed to be unreachable in the case the node is captured. In [10], the authors propose a variation of this protocol where the predeployed key is used only for a restricted period of time during which nodes establish pairwise keys. Then, the predeployed key is erased. However, Hello messages used to establish pairwise keys are sent in the clear. So, an attacker that captures a node and also eavesdrops hello messages can use the IDs and nonces contained in these messages to derive established keys.
Perrig et al. propose in [11] SPINS, a key management protocol that relies on a trusted base station to distribute keys. SPINS contains two parts: SNEP (Secure Network Encryption Protocol) that protects communications between a node and the base station or between two nodes, and  TESLA (microtime efficient streaming loss-tolerant authentication) that serves to authenticate packets coming from the base station. The first part is unsuitable to energy constraint of nodes because any communication between two nodes must pass through the base station. The second part needs additional memory space to store authentication keys. In [12], the authors propose LEAP (Localized Encryption and Authentication Protocol); a key management protocol intended to support several communication patterns. In this protocol, each node stores four types of keys: individual, pairwise, cluster, and group. An individual key is a key shared between a node and the base station. A pairwise key is shared between a node and each of its neighbors. A cluster key is a key shared between a node and all neighboring nodes. A group key is a key common to the entire network. The individual key is preloaded. After deployment, neighboring nodes establish pairwise keys. They authenticate themselves using a predeployed key which is erased as soon as pairwise keys are established. To establish cluster keys and the group key, nodes use broadcasts and message relaying. The protocol uses
TESLA (microtime efficient streaming loss-tolerant authentication) that serves to authenticate packets coming from the base station. The first part is unsuitable to energy constraint of nodes because any communication between two nodes must pass through the base station. The second part needs additional memory space to store authentication keys. In [12], the authors propose LEAP (Localized Encryption and Authentication Protocol); a key management protocol intended to support several communication patterns. In this protocol, each node stores four types of keys: individual, pairwise, cluster, and group. An individual key is a key shared between a node and the base station. A pairwise key is shared between a node and each of its neighbors. A cluster key is a key shared between a node and all neighboring nodes. A group key is a key common to the entire network. The individual key is preloaded. After deployment, neighboring nodes establish pairwise keys. They authenticate themselves using a predeployed key which is erased as soon as pairwise keys are established. To establish cluster keys and the group key, nodes use broadcasts and message relaying. The protocol uses  Tesla [11] to authenticate broadcasts.
Tesla [11] to authenticate broadcasts.
Liu et al. propose in [13] LBKs (location-based keys) that relies on location information to achieve key management. The keys are established according to the geographical location of sensor nodes. However, knowing the geographical location of nodes is not guaranteed with random deployment. Eschenauer and Gligor [14] propose a scheme based on a random key predistribution. In this scheme, each sensor randomly picks a set of keys and their identifiers from a key pool before deployment. Then, a shared-key discovery phase is launched where two neighbors exchange and compare list of identities of keys in their key chains. Basically, each sensor node broadcasts one message and receives one message from each node within its radio range where messages carry key ID lists. So, any pair of nodes has a certain probability to share at least one common key. The challenge of this scheme is to find a good tradeoff between the size of the key pool and the number of keys stored by nodes to achieve the best probability. The main drawback of this approach is that if the number of compromised nodes increases, the fraction of affected links also increases. Other solutions use the principle of probabilistic key predistribution [15, 16] introduced in [14]. For example, the authors of [16] suppose that the deployment area is a grid-based structure of  *
* cells called groups. Groups contain the same number of sensor nodes. The protocol uses
cells called groups. Groups contain the same number of sensor nodes. The protocol uses  *
* key pools such that neighboring key pools have more keys in common. Sensor nodes are deployed with the key pool that corresponds to their group in the deployment area. After deployment, nodes sharing keys can communicate directly. Nodes that do not share keys must establish a path key using their neighbors. In [15], the authors propose to increase the amount of key overlap required in the shared-key discovery phase. Their scheme called
key pools such that neighboring key pools have more keys in common. Sensor nodes are deployed with the key pool that corresponds to their group in the deployment area. After deployment, nodes sharing keys can communicate directly. Nodes that do not share keys must establish a path key using their neighbors. In [15], the authors propose to increase the amount of key overlap required in the shared-key discovery phase. Their scheme called  -composite requires
-composite requires  common keys to establish a link key. Link between a pair of sensor nodes is set as a hash of all common keys. The scheme improves resilience because the probability that a link is compromised, when a sensor node is captured, decreases, but probability of key sharing also decreases because a pair of nodes has to share
common keys to establish a link key. Link between a pair of sensor nodes is set as a hash of all common keys. The scheme improves resilience because the probability that a link is compromised, when a sensor node is captured, decreases, but probability of key sharing also decreases because a pair of nodes has to share  keys instead of one.
keys instead of one.
Eltoweissy et al. [17] propose EBS (Exclusion-based System), a key scheme that assigns each node  keys from a key pool of size
keys from a key pool of size  . If node capture is detected, rekeying occurs throughout the network. However, the authors [17] did not indicate a method for detecting a compromised node. Moreover, even if a small number of nodes in the network are compromised, information in the entire network could be discovered.
. If node capture is detected, rekeying occurs throughout the network. However, the authors [17] did not indicate a method for detecting a compromised node. Moreover, even if a small number of nodes in the network are compromised, information in the entire network could be discovered.
Section 4 summarizes the properties of these different solutions together with the proposed one within a table.
In general, existing symmetric key management solutions for WSNs focus particularly on the efficiency of key establishment after the deployment of the network. However, they do not deal with key refresh which makes key management dynamic and adds a further difficulty to the task of attackers. Furthermore, existing solutions neglect the effect of captured node attacks.
We develop in this paper a key management framework well adapted to WSNs challenges especially scalability. We focus on establishing a key refresh scheme with minimum costs that allows to deal with the resistance against the hardest attack: node compromising.
3. STKM: A Spanning Tree-Based Key Management Solution for WSNs
In this section, we describe a new key management protocol for WSNs. Our main objective is to offer a robust and simple security framework that meets the resource constraints of sensor nodes. The main idea of STKM is to build a tree in a secure manner and while conserving energy after a random deployment of nodes. Thereafter, this tree is used for rekeying to save communications. In fact, with a tree only  messages are necessary to rekey a network of
messages are necessary to rekey a network of  nodes. We begin by presenting the assumptions and notations used in the design of the solution, and then we give the detailed algorithms.
nodes. We begin by presenting the assumptions and notations used in the design of the solution, and then we give the detailed algorithms.
3.1. Assumptions and Notation
Our solution relies on the following assumptions.
-
(i)
The sensor network is static (nodes are not mobile).
-
(ii)
The sensor nodes are homogeneous: the sensor nodes are similar in their processing capacity, communication, energy, and storage.
-
(iii)
The deployment is random: the neighbors of any node are not known prior to deployment.
-
(iv)
An attacker can listen to all traffic, reflect old messages, or inject its own messages.
-
(v)
The compromise of a node implies that all information stored in its memory is known by the attacker.
-
(vi)
The base station has no constraints on the capabilities of computing, storage and cannot be compromised.
-
(vii)
The communication channels are bidirectional; if a node
 can receive a message from node
can receive a message from node  , then
, then  can send a message to
can send a message to  .
. -
(viii)
A base station which is generally the sink is responsible for initiating the key management process.
-
(ix)
Each sensor node has a unique identifier.
Table 1 shows the notations that are used to write algorithms in the remaining of the paper. Each sensor node  , including the base station, maintains the following variables.
, including the base station, maintains the following variables.
-
(i)
 : the father of the sensor in the final spanning tree. The base station is the root of the tree, so
: the father of the sensor in the final spanning tree. The base station is the root of the tree, so  is set to null.
is set to null. -
(ii)
 : the level of the sensor in the tree. The level of the root is zero, that is,
: the level of the sensor in the tree. The level of the root is zero, that is,  .
. -
(iii)
 : a list containing the identifiers of the sons of node
: a list containing the identifiers of the sons of node  within the tree.
within the tree. -
(iv)
 : a list containing the identifiers of the neighbors of node
: a list containing the identifiers of the neighbors of node  . This list is maintained to cope with node failure and node capture as described further in this section.
. This list is maintained to cope with node failure and node capture as described further in this section.
The protocol uses the following types of messages.
-
(1)
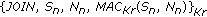
Hello, Sender ID, Sender Level,
 Sender ID, Sender Level, Sender
Sender ID, Sender Level, Sender : this message is used to construct the spanning tree. It is encrypted with the predeployed key
: this message is used to construct the spanning tree. It is encrypted with the predeployed key  . Sender ID is the identifier of the sensor node that sends the message. The Sender level is the position of the node in the tree. So, the base station which is the root of the tree is at position 0.
. Sender ID is the identifier of the sensor node that sends the message. The Sender level is the position of the node in the tree. So, the base station which is the root of the tree is at position 0. -
(2)
 ,
, New_Kr, Mal_List,
New_Kr, Mal_List, , new_
, new_ : this message initiated by the base station is used to update key
: this message initiated by the base station is used to update key  which is shared by all the sensor nodes. Mal_List is a list of nodes that are suspected to be malicious (captured nodes).
which is shared by all the sensor nodes. Mal_List is a list of nodes that are suspected to be malicious (captured nodes). -
(3)
 : this message is sent by a sensor node to the base station to request a key refresh. A node S
i
requests a key refresh when it suspects a neighbor Mal_ID to be captured.
: this message is sent by a sensor node to the base station to request a key refresh. A node S
i
requests a key refresh when it suspects a neighbor Mal_ID to be captured. -
(4)
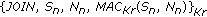
 : this message is used by a new node to join the network.
: this message is used by a new node to join the network.  is the identifier of the new node and
is the identifier of the new node and  is a nonce generated by him.
is a nonce generated by him. -
(5)
 Join-Ack,
Join-Ack, ,
, ,
,  ,
,  ,
, 
 ,
, ,
,  : this message is used by neighboring nodes to acknowledge the receipt of a Join request.
: this message is used by neighboring nodes to acknowledge the receipt of a Join request. -
(6)
 : this message is used by a new node
: this message is used by a new node  to inform surrounding nodes that its father in the spanning tree is node
to inform surrounding nodes that its father in the spanning tree is node  .
.
3.2. Algorithm
Each sensor node  is launched with three keys:
is launched with three keys:  ,
,  and
and  .
.  and
and  are shared with the base station. They both serve to secure communications between the sensor node
are shared with the base station. They both serve to secure communications between the sensor node  and the base station.
and the base station.  serves to encrypt/decrypt messages sent by
serves to encrypt/decrypt messages sent by  to the base station while
to the base station while  serves to encrypt/decrypt messages sent by the base station to
serves to encrypt/decrypt messages sent by the base station to  . The aim of using two keys is to make more difficult the task of a cryptanalysis attacker. Key
. The aim of using two keys is to make more difficult the task of a cryptanalysis attacker. Key  is shared by all nodes of the network; this key is used to encrypt (decrypt) messages immediately after deployment.
is shared by all nodes of the network; this key is used to encrypt (decrypt) messages immediately after deployment.
After deployment, each node copies its key  in its RAM (volatile memory) and removes it from its nonvolatile memory (EROM). If an attacker captures (physical access) a node after deployment, he will not have access to the key
in its RAM (volatile memory) and removes it from its nonvolatile memory (EROM). If an attacker captures (physical access) a node after deployment, he will not have access to the key  rapidly. The base station initiates the construction of the spanning tree by broadcasting a Hello message as follows:
rapidly. The base station initiates the construction of the spanning tree by broadcasting a Hello message as follows:

The purpose of this message is to discover neighboring nodes of the base station. Upon receiving the message for the first times each node  set, its father to BS and sets its level in the tree to 1. Then,
set, its father to BS and sets its level in the tree to 1. Then,  broadcasts a similar message that is,
broadcasts a similar message that is,  *:
*: Kr
, in its neighboring hood to allow other nodes to join the tree and so on until all the nodes join the tree.
Kr
, in its neighboring hood to allow other nodes to join the tree and so on until all the nodes join the tree.
When receiving other Hello messages, each node uses them to set its list of sons in the tree and computes common keys with them or simply constructs its list of neighbors. Algorithm 1 describes the detailed actions achieved by a sensor node when receiving a Hello message.
Algorithm 1
Recieve 
If the message is received for the first time Then
 := Sender_ID; /* Father receives the identifier of the sender. */
:= Sender_ID; /* Father receives the identifier of the sender. */
 := Sender_Level + 1;
:= Sender_Level + 1;
If (Fatheri BS) Then
BS) Then
/*Compute a common key with the father */
 :=
:=  (
(  );
);
/* if the father is the BS a shared key already exists.
Si → *:  ;
;
Else
If ( = Sender_Level – 1) AND (Sender_Father ==
= Sender_Level – 1) AND (Sender_Father ==  ) Then
) Then
Add the node Sender_ID to the list of sons;
If  BS then
BS then
Compute a shared key with the son Sender_ID:
 :=
:=  ;
;
EndIF
Else
Add the node  to the list of neighbors;
to the list of neighbors;
End IF
Figure 3 shows some steps of the construction of the spanning tree of the WSN depicted on Figure 1. Figure 3(a) shows the first step where the neighbors of the base station join the tree. In Figure 3(b), we only show the step during which neighbors of nodes S5 join the tree. Finally, the complete tree is depicted in Figure 3(c).
3.3. Tree Maintenance and Rekeying
Once the tree is constructed, each node shares a symmetric key with the base station, a symmetric key with its father in the tree, and the key K r with the whole network. A rekeying process is launched by the base station periodically to refresh Kr as follows.
-
(1)
The BS sends to each son S i a Refresh message encrypted with their common key

 REFRESH, BS, New_Kr, null,
REFRESH, BS, New_Kr, null,
 BS, new_
BS, new_ . Note that in a periodic refreshmal_ID is set to null. However, if the base station issues the REFRESH because of a captured node attack, it includes the ID of this node in the message.
. Note that in a periodic refreshmal_ID is set to null. However, if the base station issues the REFRESH because of a captured node attack, it includes the ID of this node in the message. -
(2)
When a son node of the base station receives the Refresh message, it updates key
 bynew_
bynew_ , then it forwards the Refresh message of the base station to its own sons. The message is encrypted with the symmetric key shared between father and son. So, the Refresh message goes downward within the tree till reaching all the sensor nodes. Thus, all sensor nodes get the new global key.
, then it forwards the Refresh message of the base station to its own sons. The message is encrypted with the symmetric key shared between father and son. So, the Refresh message goes downward within the tree till reaching all the sensor nodes. Thus, all sensor nodes get the new global key.
A rekeying process may also be trigged if malicious/captured nodes are detected in the network. Because they are resource constrained, sensor nodes cannot implement mechanisms for detecting malicious nodes. For example, putting a sensor node in promiscuous mode is not feasible. Detecting captured nodes is conceivable only if the captured node issues attacks such as sending unnecessary messages to its neighbors to cause energy depletion. When a node  suspects one of its neighbors, say
suspects one of its neighbors, say  , to be captured, two situations are possible.
, to be captured, two situations are possible.
-
(i)
If the suspected node
 is the son of
is the son of  , node S
i
ignores the messages of
, node S
i
ignores the messages of  and removes it from the list of sons. Then it generates a nonce
and removes it from the list of sons. Then it generates a nonce  and sends
and sends 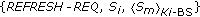 to its father on the tree. This message goes upward until it reaches the BS. This last broadcasts a refresh message
to its father on the tree. This message goes upward until it reaches the BS. This last broadcasts a refresh message  REFRESH, BS, New_Kr,
REFRESH, BS, New_Kr, BS, new_
BS, new_ in the tree. With this message,
in the tree. With this message,  is updated and all sensor nodes are aware that
is updated and all sensor nodes are aware that  is malicious.
is malicious. -
(ii)
If the suspected node
 is the father of
is the father of  , node
, node  must first contact one of its neighbors in the list
must first contact one of its neighbors in the list  to find another father and by the way another path to reach the base station. If it succeeds in this task, it issue a REFRESH-REQ as in the precedent case.
to find another father and by the way another path to reach the base station. If it succeeds in this task, it issue a REFRESH-REQ as in the precedent case.
In both cases, it is the base station that decides if it issues a key refresh or not. We suppose that the base station has more means and resources to detect malicious/captured nodes. Captured nodes may also send REFRESH-REQ messages only to consume energy and to evict honest nodes from the network. If the base station detects this behavior, it may issue a REFRESH message that evicts the node that sends the REFRESH-REQ from the network.
Adding a new node S n is achieved as follows.
-
(1)
 generates a nonce
generates a nonce  and broadcasts a join message as follows:
and broadcasts a join message as follows:  *:
*:  , The JOIN message is encrypted with the current value of
, The JOIN message is encrypted with the current value of  , the key shared by all the sensor nodes. So, the new sensor node must be launched with this key at deployment. Note here that deploying a new sensor must be synchronized with the periodic rekeying process to avoid deploying a new node with an obsolete key.
, the key shared by all the sensor nodes. So, the new sensor node must be launched with this key at deployment. Note here that deploying a new sensor must be synchronized with the periodic rekeying process to avoid deploying a new node with an obsolete key. -
(2)
When receiving the Join message, every node
 in the transmission range of the new node generates a nonce
in the transmission range of the new node generates a nonce  and responds with the following message:
and responds with the following message: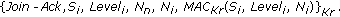 (2)
(2) -
(3)
The new node declares the source of the first received message as a father and diffuses the following message:
 .
. -
(4)
The father node adds the new son node in its sons list. The surrounding nodes that heard the Father message add the new node to their list of neighbors.
-
(5)
The father and the son compute their shared keys.
A sensor node may fail or consume totally its energy. In this case, nodes that are attached to him, especially its sons, must search for another path to the base station. So, they ask the nodes in their list of neighbors to take the place of the failed father.
4. Evaluation
4.1. Comparison with Exiting Solutions
In this section, we evaluate the performance of our solution and compare it with existing ones. We use the following metrics to achieve this evaluation.
-
(i)
Memory complexity: memory needed to store keys.
-
(ii)
Communication Complexity: number of messages exchanged for key management.
-
(iii)
Key connectivity: the probability that two nodes (or more) share a key.
-
(iv)
Resilience against node capture: this metric measures the impact of a node compromise on the security of the rest of the network. We quantify this metric with the three following values:
-
(a)
good resilience: the compromised node affects only its neighbors (local influence),
-
(b)
weak resilience: the compromised node affects its neighbors and also some nonneighboring nodes,
-
(c)
very weak resilience: if the compromise of one node leads to compromise the whole network.
-
(a)
-
(v)
Scalability: this metric measures the flexibility of the protocol with the size of the network. In other words, the metric shows how the cost of the protocol, that is memory and message overhead, varies when the network becomes larger. Scalability is a very important metric to consider when distributed algorithms are proposed, especially for dense WSNs. To quantify scalability, we use the following values:
-
(a)
very good: the protocol does not induce further costs when the number of nodes in the network increases,
-
(b)
good: the protocol induces reasonable costs when the number of nodes increases,
-
(c)
medium: the cost of the protocol depends on the number of nodes.
-
(a)
Table 2 presents the results of comparing key management protocols described in Section 2 with the proposed solution. The different notations used in the table are described in Section 2. In the proposed scheme, a node needs to store initially three keys before deployment. After deployment, each node computes a number of keys that is the function of the number of its neighbors. If a node  has d neighbors, where
has d neighbors, where  are sons, the set of keys stored by the node
are sons, the set of keys stored by the node  is two keys (with the base station)
is two keys (with the base station)  one key (shared by the whole network)
one key (shared by the whole network)  keys. The memory complexity of our solution is acceptable for nowadays sensors.
keys. The memory complexity of our solution is acceptable for nowadays sensors.
The analysis of the communication complexity for the construction of the tree is measured by the number of messages received and issued by each node. Each node sends a message and receives  messages from its neighbors, that is,
messages from its neighbors, that is,  messages by each node. Our solution has a low-complexity communication over other proposed solutions [6, 9–13], moreover, it is deterministic; key connectivity is equal to one (no concept of probability).
messages by each node. Our solution has a low-complexity communication over other proposed solutions [6, 9–13], moreover, it is deterministic; key connectivity is equal to one (no concept of probability).
Preserving energy in WSNs is very important and having a low communication complexity means that the solution minimizes energy.
4.2. Simulation Results
To validate the results presented by table II, we also measured the performance of our protocol by simulation. In this section, we provide an overview of our simulation model and some of the results we obtained. We implemented our scheme within the MATLAB framework (MATLAB for MATrix LABoritory is a matrix-based system for scientific and engineering calculation). We considered WSNs with 500 sensor nodes deployed randomly in an area of 250 * 250 meters square. Each sensor node has a signal range of 15 meters.
We first focused on evaluating the average number of messages received by a sensor node after a random deployment. This number of messages is equal to the number of neighbors of the sensor node as explained earlier. Multiple runs were conducted. Each run corresponds to a particular random deployment of the 500 identified sensor nodes. During each run, we measured the number of neighbors of each sensor node. We took the average of the values registered at the level of each sensor node. Figure 4 illustrates the obtained results. It appears that our random deployments generate an average number of neighbors at most equal to 12. If the value of energy consumed by each type of message is known, we can compute the total energy consumed during tree construction.
We then considered the resilience of our scheme to node capture. We compute the resilience to node capture by the fraction of total communication links that are compromised by the capture of x nodes. We assume that sensor nodes are randomly captured by an attacker. Figure 5 presents the obtained results. It shows that for a network of 500 sensor nodes, an attacker must capture at least 100 sensor nodes to reach all communications in the network. This corresponds to 20% of nodes in the network.
We also carried out multiple experiments on networks of size ranging from 500 to 1000 nodes. In each experiment we computed the maximum number of messages that can be received by a node. We took the average number of this value for each network size. Figure 6 summarizes these results. It shows how the number of messages received by a sensor node evolves when the size of the network becomes larger. The curve is almost logarithmic which is very acceptable.
4.3. Security Analysis
In this section, we analyze the security of our solution. As mentioned in the assumptions (cf. Section 3.1), the base station will not be compromised. An outsider attacker, who does not know the key  , cannot discover the meaning of messages diffused by nodes after deployment. Nevertheless, an attacker can compromise one or more nodes, so he becomes an insider attacker. The keys of the compromised node can be used for forging wrong messages (reading message, for example,) and also consume nodes' energy by sending useless messages to his sons and father. If the base station can detect an abnormal behavior of a node, it can lunch a rekeying to refresh
, cannot discover the meaning of messages diffused by nodes after deployment. Nevertheless, an attacker can compromise one or more nodes, so he becomes an insider attacker. The keys of the compromised node can be used for forging wrong messages (reading message, for example,) and also consume nodes' energy by sending useless messages to his sons and father. If the base station can detect an abnormal behavior of a node, it can lunch a rekeying to refresh  and revoke this node. In the following, we analyze the behavior of our solution for three types of attack.
and revoke this node. In the following, we analyze the behavior of our solution for three types of attack.
-
(1)
HELLO flood attack: in our proposal, nodes discover their neighbors by sending a HELLO message encrypted with the key
 . An attacker without knowing the key
. An attacker without knowing the key  could not launch a HELLO Flood attack.
could not launch a HELLO Flood attack. -
(2)
Sybil attack: in the algorithm, an MAC of the node's identifier, its level, and its father's identifier is calculated to authenticate the sender and the receiver. Therefore, a node cannot play a role of other nodes.
-
(3)
Node capture attack: when a node is captured, this does not affect its neighbors. In fact, after a node is captured, what can an attacker do? Since he has the key shared with the base station, he may send wrong information (lectures) to that base station. The latter may have a mechanism to verify the behavior of sender nodes. The attacker also has access to the keys of the sons of the victim enabling it thereafter to send unnecessary messages to these sons in order to consume their energy and cause battery depletion. Nodes that detect these useless messages can suspect the captured node and inform the base station with a REFRESH-REQ message.
5. Conclusion
Security is a necessity for most applications using WSNs, especially if the sensor nodes are deployed in unsafe areas, such as battlefields, strategic places (airports, critical buildings ). These sensor nodes operating in difficult access places, without protection and without possibility of recharging their batteries, may be subject to disruptive and malicious actions. Therefore, it is important to provide to them an acceptable security level. The primary objective of WSN nodes is to collect data and transmit them to a decision center. So, this must be done in a trustworthy and safe way. In this paper, we presented a key management solution to WSN that deals with one of the hardest attack: node capture. The main idea of the solution is to quickly and cheaply build a spanning tree that serves to refresh the shared key with minimum costs. The solution is scalable and uses little memory.
). These sensor nodes operating in difficult access places, without protection and without possibility of recharging their batteries, may be subject to disruptive and malicious actions. Therefore, it is important to provide to them an acceptable security level. The primary objective of WSN nodes is to collect data and transmit them to a decision center. So, this must be done in a trustworthy and safe way. In this paper, we presented a key management solution to WSN that deals with one of the hardest attack: node capture. The main idea of the solution is to quickly and cheaply build a spanning tree that serves to refresh the shared key with minimum costs. The solution is scalable and uses little memory.
As a perspective of our present work, we plan to use the NS2 simulator to compare the performance of our solution with other solutions from the literature. We also work on a mobile version of our scheme.
References
Akyildiz IF, Su W, Sankarasubramaniam Y, Cayirci E: A survey on sensor networks. IEEE Communications Magazine 2002, 40(8):102-114. 10.1109/MCOM.2002.1024422
Kavitha T, Sridharan D: Security vulnerabilities in wireless sensor networks: a survey. Journal of Information Assurance and Security 2010, 5: 31-44.
Xiao Y, Rayi VK, Sun B, Du X, Hu F, Galloway M: A survey of key management schemes in wireless sensor networks. Computer Communications 2007, 30(11-12):2314-2341. 10.1016/j.comcom.2007.04.009
Watro RJ, Kong D, Cuti S-F, Gardiner C, Lynn C, Kruus P: TinyPK: securing sensor networks with public key technology. Proceedings of the 2004 ACM Workshop on Security of Ad Hoc and Sensor Networks (SASN '04), October 2004 59-64.
Ning P, Liu A: TinyECC: elliptic curve cryptography for sensor networks. http://discovery.csc.ncsu.edu/software/TinyECC/
Anderson R, Chan H, Perrig A: Key infection: smart trust for smart dust. Proceedings of the 12th IEEE International Conference on Network Protocols (ICNP '04), October 2004 206-215.
Blom R: An optimal class of symmetric key generation systems. In Proceedings of the Eurocrypt 84 Workshop on Advances in Cryptology: Theory and Application of Cryptographic Techniques, 1985. Springer; 335-338.
Blundo C, Santix AD, Herzberg A, Kutten S, Vaccaro U, Yung M: Perfectly-secure key distribution for dynamic conferences. In Proceedings of the 12th Annual International Cryptology Conference on Advances in Cryptology, 1992, Berlin, Germany. Spring; 471-486.
Lai B, Kim S, Verbauwhede I: Scalable session key construction protocol for wireless sensor networks. Proceedings of the IEEE Workshop on Large Scale RealTime and Embedded Systems (LARTES '02), 2002
Dutertre B, Cheung S, Levy J: Lightweight key management in wireless sensor networks by leveraging initial trust. SDL Technical Report SRI-SDL-04-02 2004.
Perrig A, Szewczyk R, Wen V, Culler D, Tygar JD: SPINS: security protocols for sensor networks. In Proceedings of the 7th Annual International Conference on Mobile Computing and Networking, July 2001. ACM Press; 189-199.
Zhu S, Setia S, Jajodia S: LEAP: efficient security mechanisms for large-scale distributed sensor networks. Proceedings of the 10th ACM Conference on Computer and Communications Security (CCS '03), October 2003 62-72.
Liu D, Ning P: Location-based pairwise key establishments for static sensor networks. Proceedings of the 1st ACM Workshop on Security of Ad Hoc and Sensor Networks (CCS '03), October 2003 72-82.
Eschenauer L, Gligor VD: A key-management scheme for distributed sensor networks. Proceedings of the 9th ACM Conference on Computer and Communications Security, November 2002 41-47.
Liu D, Ning P, Rongfang LI: Establishing pairwise keys in distributed sensor networks. ACM Transactions on Information and System Security 2005, 8(1):41-77. 10.1145/1053283.1053287
Du W, Deng J, Han YS, Chen S, Varshney PK: A key management scheme for wireless sensor networks using deployment knowledge. Proceedings of the IEEE International Conference on Computer Communications (IEEE INFOCOM '11), March 2004 586-597.
Eltoweissy M, Moharrum M, Mukkamala R: Dynamic key management in sensor networks. IEEE Communications Magazine 2006, 44(4):122-130.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
Open Access This article is distributed under the terms of the Creative Commons Attribution 2.0 International License ( https://creativecommons.org/licenses/by/2.0 ), which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.
About this article
Cite this article
Messai, M.L., Aliouat, M. & Seba, H. Tree Based Protocol for Key Management in Wireless Sensor Networks. J Wireless Com Network 2010, 910695 (2010). https://doi.org/10.1155/2010/910695
Received:
Accepted:
Published:
DOI: https://doi.org/10.1155/2010/910695


 can receive a message from node
can receive a message from node  , then
, then  can send a message to
can send a message to  .
. : the father of the sensor in the final spanning tree. The base station is the root of the tree, so
: the father of the sensor in the final spanning tree. The base station is the root of the tree, so  is set to null.
is set to null. : the level of the sensor in the tree. The level of the root is zero, that is,
: the level of the sensor in the tree. The level of the root is zero, that is,  .
. : a list containing the identifiers of the sons of node
: a list containing the identifiers of the sons of node  within the tree.
within the tree. : a list containing the identifiers of the neighbors of node
: a list containing the identifiers of the neighbors of node  . This list is maintained to cope with node failure and node capture as described further in this section.
. This list is maintained to cope with node failure and node capture as described further in this section. Sender ID, Sender Level, Sender
Sender ID, Sender Level, Sender : this message is used to construct the spanning tree. It is encrypted with the predeployed key
: this message is used to construct the spanning tree. It is encrypted with the predeployed key  . Sender ID is the identifier of the sensor node that sends the message. The Sender level is the position of the node in the tree. So, the base station which is the root of the tree is at position 0.
. Sender ID is the identifier of the sensor node that sends the message. The Sender level is the position of the node in the tree. So, the base station which is the root of the tree is at position 0. ,
, New_Kr, Mal_List,
New_Kr, Mal_List,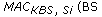 , new_
, new_ : this message initiated by the base station is used to update key
: this message initiated by the base station is used to update key  which is shared by all the sensor nodes. Mal_List is a list of nodes that are suspected to be malicious (captured nodes).
which is shared by all the sensor nodes. Mal_List is a list of nodes that are suspected to be malicious (captured nodes).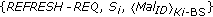 : this message is sent by a sensor node to the base station to request a key refresh. A node S
i
requests a key refresh when it suspects a neighbor Mal_ID to be captured.
: this message is sent by a sensor node to the base station to request a key refresh. A node S
i
requests a key refresh when it suspects a neighbor Mal_ID to be captured.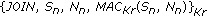 : this message is used by a new node to join the network.
: this message is used by a new node to join the network.  is the identifier of the new node and
is the identifier of the new node and  is a nonce generated by him.
is a nonce generated by him. Join-Ack,
Join-Ack, ,
, ,
,  ,
,  ,
, 
 ,
, ,
,  : this message is used by neighboring nodes to acknowledge the receipt of a Join request.
: this message is used by neighboring nodes to acknowledge the receipt of a Join request.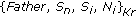 : this message is used by a new node
: this message is used by a new node  to inform surrounding nodes that its father in the spanning tree is node
to inform surrounding nodes that its father in the spanning tree is node  .
.

 REFRESH, BS, New_Kr, null,
REFRESH, BS, New_Kr, null,
 BS, new_
BS, new_ . Note that in a periodic refreshmal_ID is set to null. However, if the base station issues the REFRESH because of a captured node attack, it includes the ID of this node in the message.
. Note that in a periodic refreshmal_ID is set to null. However, if the base station issues the REFRESH because of a captured node attack, it includes the ID of this node in the message. bynew_
bynew_ , then it forwards the Refresh message of the base station to its own sons. The message is encrypted with the symmetric key shared between father and son. So, the Refresh message goes downward within the tree till reaching all the sensor nodes. Thus, all sensor nodes get the new global key.
, then it forwards the Refresh message of the base station to its own sons. The message is encrypted with the symmetric key shared between father and son. So, the Refresh message goes downward within the tree till reaching all the sensor nodes. Thus, all sensor nodes get the new global key. is the son of
is the son of  , node S
i
ignores the messages of
, node S
i
ignores the messages of  and removes it from the list of sons. Then it generates a nonce
and removes it from the list of sons. Then it generates a nonce  and sends
and sends 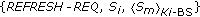 to its father on the tree. This message goes upward until it reaches the BS. This last broadcasts a refresh message
to its father on the tree. This message goes upward until it reaches the BS. This last broadcasts a refresh message  REFRESH, BS, New_Kr,
REFRESH, BS, New_Kr, BS, new_
BS, new_ in the tree. With this message,
in the tree. With this message,  is updated and all sensor nodes are aware that
is updated and all sensor nodes are aware that  is malicious.
is malicious. is the father of
is the father of  , node
, node  must first contact one of its neighbors in the list
must first contact one of its neighbors in the list  to find another father and by the way another path to reach the base station. If it succeeds in this task, it issue a REFRESH-REQ as in the precedent case.
to find another father and by the way another path to reach the base station. If it succeeds in this task, it issue a REFRESH-REQ as in the precedent case. generates a nonce
generates a nonce  and broadcasts a join message as follows:
and broadcasts a join message as follows:  *:
*:  , The JOIN message is encrypted with the current value of
, The JOIN message is encrypted with the current value of  , the key shared by all the sensor nodes. So, the new sensor node must be launched with this key at deployment. Note here that deploying a new sensor must be synchronized with the periodic rekeying process to avoid deploying a new node with an obsolete key.
, the key shared by all the sensor nodes. So, the new sensor node must be launched with this key at deployment. Note here that deploying a new sensor must be synchronized with the periodic rekeying process to avoid deploying a new node with an obsolete key. in the transmission range of the new node generates a nonce
in the transmission range of the new node generates a nonce  and responds with the following message:
and responds with the following message: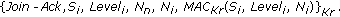
 .
.


 . An attacker without knowing the key
. An attacker without knowing the key  could not launch a HELLO Flood attack.
could not launch a HELLO Flood attack.